Practical Steps for Organizations to Use the New Standard Contractual Clauses

The European Commission adopted new versions of the Standard Contractual Clauses (SCCs) on June 4, 2021. The new SCCs finally replace the original SCCs adopted under the 1998 European Data Protection Directive (DPD) and did not completely meet the requirements of the General Data Protection Regulation (GDPR) passed in 2016. For example, the scope of the DPD only applied to data controllers in the European Union (EU) or European Economic Area (EEA), and the original SCCs assumed that the controller was always in the EU or the EEA and was the entity exporting the personal data. However, the scope of the GDPR is significantly broader than the DPD. It may apply to organizations physically located outside of the EU or EEA when they offer their goods and services to individuals located in the EU or EEA. Controllers located outside of the EU or EEA that used the original SCCs to facilitate transfers to processors located within the EU or EEA were required to sign off as a “data exporter,” while data processors were left to be classified as “data importers.” The new SCCs seek to fix this by applying to a more diverse set of situations, accounting for the reality of processors and controllers located within or outside of the EU or EEA.
The new SCCs provide a much-needed update to the SCCs, incorporating new clauses directed at supplemental security measures and additional assessments for cross-border data transfers required due to the Schrems II decision. In particular, the SCCs now require that organizations conduct a transfer impact assessment (TIA) to evaluate the protections for personal data in the importing countries. The TIA is consistent (and effectively codifies) the guidance provided by the European Data Protection Board in December 2020 and recently updated on June 21, 2021:
- Clause 14 requires that organizations conduct a TIA, document the circumstances of the transfer, the governing laws of the importing country, the likelihood of the data being subject to such requests, and the supplemental security measures that the parties will adopt to protect against unwanted disclosure of the personal data. The new guidance issued now allows organizations to conduct a subjective assessment regarding the adequacy of the transfer (e.g., when determining the likelihood of personal data being accessed by law enforcement and other public authorities, how the sensitivity of such data affects risk, etc.). A new footnote states, “[s]uch elements may include relevant and documented practical experience with prior instances of requests for disclosure from public authorities, or the absence of such requests.”
- Similarly, Clause 15 obligates the importing party to maintain records of and notify the data exporter when it receives a request for access to the information from public authorities in the importing country whenever possible. The data importer is also obligated to challenge any requests from public authorities and utilize available appeals processes. The new SCCs require that the data importer implement data minimization measures, so the data importer only provides the minimum amount of personal data to satisfy the request.
 The new SCCs went into effect June 27, 2021, 20 days after publication in the Official Journal of the European Union (the OJ) on June 7, 2021 (OJ L 199/31). On September 27, 2021, three months after the new SCCs go into effect (the “Repeal Date”), the old SCCs will officially be considered repealed and invalid for use in new agreements. After this date, all new agreements are required to use the new SCCs. All existing agreements using the current SCCs will continue to be valid until December 27, 2022, 18 months after the SCCs are published in the OJ.
The new SCCs went into effect June 27, 2021, 20 days after publication in the Official Journal of the European Union (the OJ) on June 7, 2021 (OJ L 199/31). On September 27, 2021, three months after the new SCCs go into effect (the “Repeal Date”), the old SCCs will officially be considered repealed and invalid for use in new agreements. After this date, all new agreements are required to use the new SCCs. All existing agreements using the current SCCs will continue to be valid until December 27, 2022, 18 months after the SCCs are published in the OJ.
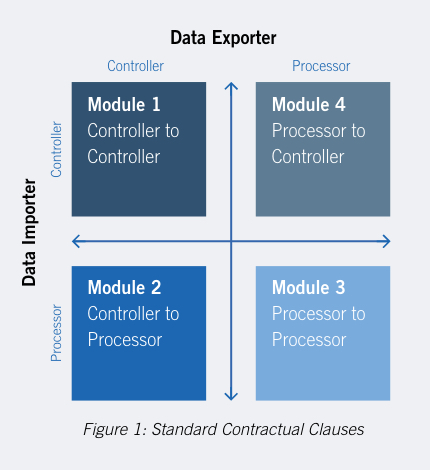
While the new SCCs were designed as separate documents, the new SCCs consist of four “modules,” one for each transfer situation (i.e., Controller-Controller, Controller-Processor, Processor-Processor, Processor-Controller – see Figure 1). The SCCs also have several optional clauses. Thus, while finally taking into account the requirements of the GDPR, the new SCCs are still challenging to work with, and organizations should begin the painstaking tasks of adoption sooner rather than later.
Steps Organizations Can Take
We recommend that organizations that rely on the SCCs to lawfully transfer information from the EU or EEA immediately begin to take the following steps in the order of priority that makes practical sense for your organization:
- Review existing contracts to determine the priority of relationships to be addressed. While the SCCs do not provide exemptions for migrating between the current and the new SCCs, it will take time and effort for some organizations to complete the transition due to the level of effort required and the number of contracts that are required to be addressed. As a result, priority should be given to those contracts that demonstrate a greater level of risk. The audit should cover all internal and external relationships and data transfers.
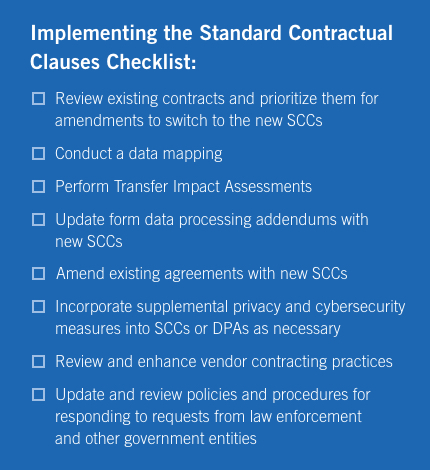 Conduct a data mapping to understand the country(ies) that data is exported from and imported into. Organizations should immediately review and map all transfers of personal data from outside the EU and EEA to understand the location and direction of the flow of personal data and the roles that each party plays in the processing (controller, processor, or both). This should not only include any physical transfer of personal data but also include transfers that result from incidental activities such as backup, support, and remote access outside the EU and EEA.
Conduct a data mapping to understand the country(ies) that data is exported from and imported into. Organizations should immediately review and map all transfers of personal data from outside the EU and EEA to understand the location and direction of the flow of personal data and the roles that each party plays in the processing (controller, processor, or both). This should not only include any physical transfer of personal data but also include transfers that result from incidental activities such as backup, support, and remote access outside the EU and EEA.- Transfer Impact Assessments. Organizations should conduct and document TIA’s following the guidance provided by the European Data Protection Board. This may be a significant effort for organizations as they now must: (a) assess and understand the laws of the importing country, and (b) determine whether (i) such laws afford the personal data a level of protection that are essentially equivalent to those that the GDPR provides; or (ii) if additional technical, organizational, or contractual measures may need to be taken. In particular, the new SCCs require that all parties warrant that “they have no reason to believe that the laws and practices in the third country of destination applicable to the processing of the personal data by the data importer, including any requirements to disclose personal data or measures authorizing access by public authorities, prevent the data importer from fulfilling its obligations under these Clauses.” In many cases, this may require collaboration with experts in the importing country’s national security and surveillance laws. It is also crucial that the organization conduct such a TIA for each country that may import personal data from the EU and EEA and each level of sensitivity of the personal data, considering the existing safeguards already in place. For example, the TIA should be conducted separately for customer data, which may consist of simple contact information like names and email addresses, then the TIA prepared for employee information, even when both types of data are imported into the same country (and sometimes even by the same data importer). In conducting the TIA, the parties must also account for “the specific circumstances of the transfer, including the length of the processing chain, the number of actors involved and the transmission channels used; intended onward transfers; the type of recipient; the purpose of the processing; the categories and format of the transferred personal data; the economic sector in which the transfer occurs; the storage location of the data transferred.” The TIA should be documented as one may be required to make it available to the supervisory authorities upon request.
- Update form agreements with new SCCs. Organizations should update their form data processing addendums and other agreements that contemplate transferring personal data outside of the EU or EEA with the new SCCs. This may include such agreements currently being negotiated and likely to be executed after September 27, 2021. Companies should be careful to use the correct modules of the new SCCs and remove the modules that do not apply to the processing activities. Organizations should also be aware that, when processing both as controllers and processors, multiple modules or multiple versions of the SCCs may be appropriate.
-
Amend existing agreements with new SCCs. Organizations should immediately inventory and assess all third-party agreements that include transferring personal data from the EU or EEA and prioritizing the most critical ones based on the nature, sensitivity, and volume of information. Although organizations have until December 27, 2022, before the new SCCs are required in existing agreements, there is a significant amount of work to adopt the new SCCs. Organizations should also take this opportunity to prioritize any agreements they discover that perhaps should have had SCCs (or that may have relied on the now-invalid Privacy Shield) but have still not been amended. While tempting to do so, one or both parties may seek to use this as an opportunity to open up the agreement for renegotiation, perhaps as an attempt to shift some of the existing or new risks to the other party. This may occur through revisions to indemnification, limitations of liability, and other similar clauses. The parties should refrain from any such changes as they may adversely impact or create new conflicts with the SCCs. Here again, organizations should be careful to use the correct modules of the SCCs based on the locations of the parties.
- Incorporate supplemental privacy and cybersecurity measures into the SCCs as necessary. Data exporters, whether as a processor or a controller, are ultimately responsible for assessing the effectiveness of the protections for the transfer on a case-by-case basis. The results of the TIA may reveal that the parties may have to adopt supplemental privacy and cybersecurity measures for particular processing activity.
- Review and enhance vendor contracting practices. Organizations should develop a process to conduct due diligence on their vendors and develop contracting practices specifically for agreements that include transferring personal information from the EU or EEA. The process must include regular review and monitoring of the vendor’s security measures to ensure they remain in compliance and that such measures remain sufficient to comply with the requirements set forth by the SCCs. The parties should document the specific organizational and technical safeguards that are being used and required by the (sub)processor to assist the data controller or exporter, as applicable.
- Update and review policies and procedures for responding to requests from law enforcement and other government entities. Organizations should be reminded that they are always required to comply with any lawful request from law enforcement or other government entities. However, the new SCCs may require organizations to notify the data exporter when they receive such requests and object to any prohibition on notifying the data exporter of such request, determine the legality of such request and object to such requests if appropriate, appeal or object to any decisions that continue to require the production of personal data as appropriate, and, to the extent necessary to disclose personal data, comply with the obligations of data minimization. Organizations should evaluate their rights and obligations under applicable laws and put policies and procedures in place so that the organization fully understands how to respond to such requests.
While the SCCs are well overdue, adopting them brings new challenges for organizations. Therefore, organizations are encouraged to start immediately adopting the new SCCs and not wait until the SCCs are no longer valid before incorporating them in new and existing agreements. As a reminder, all efforts undertaken to comply with the new SCCs should be documented as one may be required to produce it to the supervisory authorities.
The above recommendations are directed at organizations seeking to comply with the new SCCs under the GDPR. For organizations seeking to transfer data under the Data Protection Act of 2018 and UK GDPR should continue to rely on the previous SCCs. The ICO has stated that it will issue its own SCCs and guidance for data transfers later in 2021.
For more information about how to comply with these new international data transfer requirements generally, as well as steps to take toward adopting the new SCCs, please contact one of the authors listed below or any of the Partner or Senior Counsel core members of Foley’s Cybersecurity Practice.







